How to Increase Your Level of Online Privacy in Addition to Using a Cryptocurrency

Ever since cryptocurrency first made itself known to the public a few years ago, many users have switched over to try to reduce their online presence (too much success). There are many different varieties, and while all of them have their benefits and disadvantages, they all help you stay private online.
Yet is it enough? If you care about privacy, then half-measures aren’t going to do it. There are other aspects of your online life that deserve a look, and perhaps there are other ways you can help shroud yourself online. Even your current cryptocurrency use can be improved upon.
Here are a few things cryptocurrency users might want to consider to increase their privacy online even further:
Eraser, AdBlock Plus, and Cryptocat
There are plenty of privacy tools online to help you when you are using cryptocurrency in general. Here are a few specific ones worth consideration:
- If the recycle bin is a trash bin for you to throw paper balls into and emptying it is the equivalent is going out to the recycling bin on your sidewalk, then Eraser is the incinerator you have locked up in your garage for special occasions (or fun). It deletes every trace from your computer whatever file you need to be gone, and that is a handy thing to have.
- You’ve almost certainly heard of AdBlock Plus before and use it to get past pesky ads when streaming video and browsing blogs, but there is more to it than that. Those ads will often contain tracks or malware in them if you click on them (or, in the worst case scenarios, when they load), so they should be in the toolkit of any privacy-oriented internet user.
- Cryptocat is an encrypted chat tool that, while not perfect, is a major step up from many of the messengers used daily by millions. You do not want the details of your messages to be released while conducting business, and this aids in that endeavor. You should still be wary of address tracking and trust the person on the other end, though.
Use a Virtual Private Network
If you are using a public network without any protection, then there is no way you can consider yourself having a private online presence. The reasoning behind this is that there are many cyber criminals who like to sit in public places, such as cafes, and intercept data sent over private networks.
Such data can include account information, passwords, personal details, and financial information. Even if your cryptocurrency protocols are the safest available, they won’t help you when your bank account information is stolen. Public networks are a one-way ticket to identity theft, and you need protection.
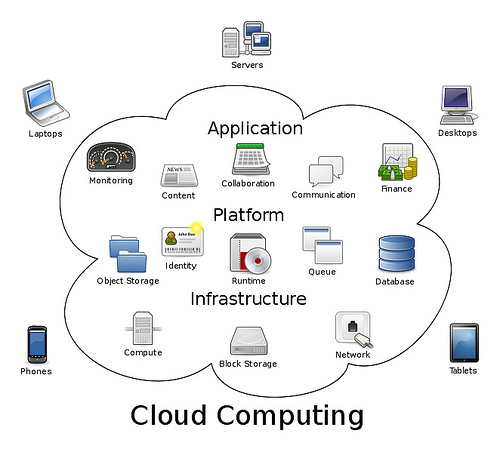
Fortunately, there are services called Virtual Private Networks (VPN) that allow you to connect your computer or device to an offsite secure server. This is done with an encrypted connection that all VPNs have which means you will be safe on public networks.
It effectively acts like a tunnel that your private information travels through, and all a hacker (or any person or organization) could find out is that you are using one. On top of this, connecting to a remote server means that your IP address will be masked, allowing you to remain untracked online.
All you need to do is find one of the best privacy-focused VPNs, and you will be safe to surf wherever you are.
Cryptonote
If you are already using cryptocurrency, then you will probably want to add to the privacy that it already provides. This is what Cryptonote can do for you.
If you are making an online transaction and want to make it untraceable, then it will handle that for you and do so in so many redundant ways you’ll start laughing.
Without going too deep into the technology (we’d be here all day), it will allow someone to pay on behalf of a group without individual identification, prevent tracking of payments received, create additional keys that act as privacy buffers, and allow no one to know your total income.
Their website is also a useful resource to explain a lot of the details of cryptocurrency for the uninitiated, and if you are technically skilled, then you should know that the organization itself is relatively transparent, allowing you to trust the technology.
Be Wary of False Privacy with Some Tools
As much as you need to use the right tools when working with cryptocurrency, you need to be wary of the wrong tools and the tools that will lead you down the wrong path. There are plenty of options available online, and some of the most popular ones won’t make you nearly as private as you think they will.
Here are a few of the top tools and techniques you should be wary of:
- There are at least a million Tor users active each and every day, but that does not mean that you are safe from detection while using it. It certainly helps, but using it will effectively put a giant bull’s eye on your back that tells governments and organizations “Hey, we should look out for this person. They might be up to something.” This puts your other online activities under scrutiny. In addition to this, organizations with sufficient resources will be able to know what you are doing by monitoring the traffic of end nodes (which they often control). If you need any more evidence, just search for XKeyscore and read what you find.
- Proxy servers are useful in certain circumstances that don’t require complete security, but they shouldn’t be wholly relied on, especially if you are using them for free. Many of the free proxy services collect user data to sell wholesale to data-mining companies, and others are unreliable at best. For a chance at privacy, you will get a headache or a data leak. There is no such thing as a free lunch.
- It is not recommended to use cloud services with cryptocurrencies in the first place, but if you are storing related data or digital purchases, the standard services you hear about in the news (OneDrive, Dropbox, Google Drive) aren’t reliable. They are often beholden to government bodies or their own interests, and they likely won’t have qualms searching through your data. If you are going to use a cloud storage solution, then it is best to use one with user-end encryption, such as Tresorit or Carbonite, so that you won’t have to worry about anyone taking a peek.

Image courtesy of BTC Keychain under CC BY 2.0
There are always new facets to be uncovered when it comes to cryptocurrency and the concept of online privacy is one that is always changing. Do you have any other tips that you use to keep yourself safe and private online? Do you have any stories or experiences that you think might be useful to others? Leave a comment below and tell us what you think.
About the Author: Cassie Philips is a cybersecurity expert and technology enthusiast for Secure Thoughts who enjoys sharing her knowledge with others. For some great tips on how you can protect yourself online, follow Cassie on Twitter.